An analyst in computer systems is responsible for planning and designing computer systems and collaborating with managers to ensure efficient use of resources. These specialists identify the kinds of hardware and software that are needed to accomplish specific tasks. Then they create flow charts to explain the logic of a system. While the job of computer systems analysts can vary in scope, many computer professionals share similar skills. They also have extensive knowledge of the latest computer technologies and may work in any area, including the Internet.
A systems analyst typically works with computers to help design new applications and improve existing ones. They may also assist in the development of new technology or perform cost-benefit analyses when considering possible upgrades to existing computer systems. They are also responsible for providing technical and business expertise to developers and engineers, and may even be involved in post-implementation troubleshooting. Systems analysts have many responsibilities. They must understand the business goals and requirements of their clients.

A master's degree in computer systems analysis may be required depending on the company and its goals. Popular options include a BSc in computer science or information systems. A graduate may choose to pursue an MBA degree in computer systems management. This could help them improve their job prospects. Some companies prefer advanced degrees for computer system analysts. A master's degree is a good choice if you are interested in a career with high potential. These degrees can be tailored to your needs and budget.
Computer systems analysts use different techniques to develop and design computer system. They create rules to govern the way computer systems present and communicate data. They must have a working knowledge about computer memory, speed, or other factors that could impact a company's operation. A computer systems analyst must be able to analyze data, and recommend cost-effective solutions that will increase the company's productivity. The computer systems analyst will work closely with managers and software developers to make sure that the changes are implemented and maintained compatibility.
Computer Systems analysts are responsible for analyzing and implementing new tools. They may also be responsible for training non-IT staff. A computer systems analyst may be required to perform network downtime preparations. Computer systems analysts are available to answer employees' questions and discuss their business needs. Computer systems analysts will ultimately be responsible for the implementation of new software and hardware and for managing all aspects. They are required to keep accurate records about every aspect of the projects.
Career prospects for computer systems analysts are good. The Bureau of Labor Statistics predicts that the industry will see 21% job growth in the next seven decades, which is significantly faster than for all other occupations. Increased IT-related services will increase the need for computer systems analysts. Many organizations have begun to outsource traditional IT analyst tasks. The Bureau of Labor Statistics also expects job growth in information technology and related services. And if all these factors are correct, this means that the job market for computer systems analysts will remain high.
FAQ
What are the future trends of cybersecurity?
Security industry is growing at an unparalleled rate. Technology is changing rapidly. Older technologies are updated and new ones are becoming obsolete. At the same time, the threats we face are constantly changing as well. Our experts have the right information for you.
Here you will find all the information you need:
-
Check out the most recent news regarding new vulnerabilities or attacks
-
Use best practice strategies to combat the latest threats
-
How to stay ahead of the curve
There are many things you can look forward to in the future. There is no way to know what lies beyond. We can only plan for what lies ahead and hope that luck will prevail.
If you want to see the future, you can read the headlines. They inform us that hackers and viruses aren't the greatest threat at present. Instead, it's governments.
Governments around the world are continuously trying to spy on their citizens. They use advanced technology (including AI) to monitor activity online and track people's movements. They collect data on everyone they come across to build up detailed profiles of individuals and groups. They don't believe privacy is important because they view it as a threat to national security.
This power can be used to target specific people by government agencies. In fact, some experts believe that the National Security Agency has already used its powers to influence elections in France and Germany. Although we don't know if the NSA targeted these countries intentionally or not, it makes sense when you consider it. You must make sure they don't stand between you and your goal to control the people.
This is not a hypothetical scenario. History shows us that dictatorships have been known to target their opponents by hacking their phones and stealing their data. It seems as though there are no limits to what governments will do in order keep their subjects under control.
Even if surveillance isn't an issue at the government level, it might be a concern about corporate spying. There's no evidence that big businesses may be tracking your every move online. For example, Facebook tracks your browsing history regardless of whether you've given permission or not. Google claims that it doesn't sell data to advertisers. But, Google has no proof.
You need to be concerned about what can happen when governments get involved. However, you should also consider how to protect your self when dealing with corporations. Learn cybersecurity if your goal is to work as an IT professional. By learning cybersecurity, you can help companies prevent access to sensitive information. You can also train employees to recognize potential phishing schemes.
Cybercrime is the number one problem in our society. Cybercriminals, hackers and criminals work together constantly to steal your personal details and compromise your computer systems. There are solutions to every problem. All you have to do to get started is to discover where to start.
What is the length of a course in cyber security?
Cybersecurity training courses typically last between six and 12 weeks, depending on how much time you have available for study. If you are looking for a short-term course you may be interested in an online one such as University of East London’s Cyber Security Certificate Program. The program meets three days per week and lasts four consecutive weeks. You can also opt for the full-time immersive option if you have several weeks to spare. This program includes lectures in class, assignments, and group discussion. These are all meant to give you a deep understanding of cybersecurity. It's easy to budget as the tuition fee includes accommodation, meals (including textbooks), and IT equipment. In addition to learning the fundamentals of cybersecurity from scratch, students also learn practical skills such as penetration testing, network forensics, ethical hacking, incident response, and cryptography. A certificate is also awarded to students upon successful completion. This program is not only designed to help people get started in cybersecurity but also helps them find jobs after graduation.
A shorter course can be finished in two years. That's the best part. However, if you're interested in long-term training, then you'll probably have to put in more effort. Although you'll spend most of the time studying, you'll also have to attend regular classes. Additionally, a longer course will cover topics like vulnerability assessment as well as digital forensics and encryption. You will need to devote at least six hours per day to your study if this is the route you choose. It is also important to show up for scheduled meetings. These can be held in person or online using platforms like Skype, Google Hangouts, and other similar tools. These may be mandatory depending on where you live.
Your choice of a full or part-time program will determine the length of your course. Part-time programs tend to run for fewer weeks, so you might only see half of the curriculum. Full-time programs typically require more intensive instruction. Therefore, they are likely to be spread across multiple semesters. Whatever your choice, make sure your course has flexible scheduling options that allow you to fit it in your busy schedule.
What makes cybersecurity different from other areas?
Cybersecurity is quite different than other IT areas where you might have faced similar problems. Many businesses use databases and servers to manage their data. Perhaps you have even worked on a project that involved website design.
These types of projects don't typically fall under the cybersecurity umbrella. Although you could still use the principles of web development for solving problems, it would likely require more than one person.
It is important to study cybersecurity. This includes learning how analyze a problem to determine whether it's due to vulnerability or something else. This will include understanding the basics and principles of encryption and cryptography. You will also need to be able to code well.
This area will be required to help you become a cybersecurity specialist. But don't forget to keep up with your core subject.
It is important to not only be able and able to process complex information but also to learn how to effectively communicate. Strong communication skills will be required both verbally as well as written.
It is important to be aware of the best practices and industry standards within your chosen career. These standards and best practices are important to ensure you don't fall behind but move forward.
How do I prepare myself for my certification exams
There are many options for how to prepare. There are many ways to prepare. One is to thoroughly study the syllabus before taking the exam. An alternative is to carefully read the exam guidebook prior to sitting the exam. You can also attempt a few sample questions in order to test your understanding of the topics covered. A local community college could be a good option. There you will have the opportunity to meet other students who have passed the certification exam.
Many websites offer free exam preparation materials. Although you can purchase the exam manual electronically, only one copy will be sent to you. This exam manual can also be purchased electronically, but only one copy is available.
Some companies even offer self-study guides. These usually cost between $100 and $400. These include flashcards and quizzes, as well as other features. Some products let you take the exam on-line.
What should you look for in a cyber security course selection?
There are many types of cyber security courses, from short courses to long-term programs. Here are some things to consider when choosing the right one. These are some of the things you should consider:
-
Which certification level would you like? Some courses offer certificates upon successful completion, while others provide diplomas or degrees. Certificates are often easier to obtain, but diplomas and degrees are generally considered more prestigious.
-
How many weeks/months will you be able to finish the course? Courses typically last 6-12 weeks. Some courses may take longer.
-
Do you prefer face-to–face interaction or distance-learning? While face-to-face classes are great for meeting other students, they can also be costly. Distance learning is a great way to save money and work at your own pace.
-
Are you looking for a job change? Or just a refresher course? For career changers, who may already be working in a different field, a brief course can help to refresh their skills and knowledge. Others may be looking for a refresher course before applying to a new job.
-
Is the course accredited Accreditation assures that a course's reliability and credibility. Accreditation guarantees that your money will not be wasted on courses that do not deliver the results you expected.
-
Do you offer internships or other placements as part of the course? Internships allow you to apply what you've learned during the class and get real-world experience working with IT professionals. You will have the opportunity to work with cybersecurity professionals and gain valuable experience.
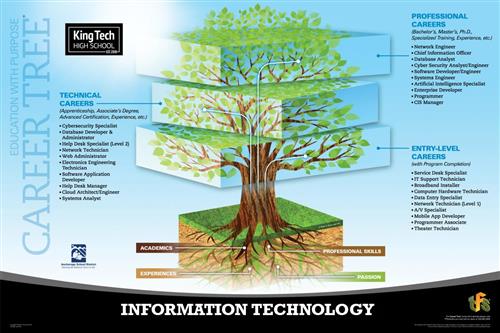
What job opportunities are there in information technology
The most common career choices for people who want to enter IT-related careers include software developer, database administrator, network engineer, systems analyst, web designer/developer, help desk support technician, computer technician, etc. Other IT-related careers include data entry clerk, sales representative and receptionist, customer support specialist, programmer/technical writer, graphic artist manager, office manager, project manger, etc.
Most people work in the field once they have graduated from school. While you are studying for your degree, you may be offered an internship with a company. A formal apprenticeship scheme is another option. This allows you to gain hands-on experience by completing work placements under supervision.
Information Technology offers many opportunities, as we have already mentioned. While not all positions require a bachelor's, most require a postgraduate qualification. For example, a master's degree (MSc) in Computer Science or Software Engineering (SSE) gives a person better qualifications than a bachelor's degree.
Some employers prefer candidates who have previous experience. Ask people you know who work in IT what positions they've been offered. To see if there are vacancies, you can also search online for job boards. You can search by area, industry, type, role, skills needed, salary range and many other options.
Try using sites like Monster.com, Simply Hired.com or Career Builder to help you find work. Join professional associations, like the American Society for Training & Development ("ASTD"), the Association for Computing Machinery ("ACM"), the Institute of Electrical and Electronics Engineers [IEEE]), etc.
Is the Google IT certificate worth it?
Google IT certification (recognized by the industry) is a credential for web designers and developers. This certification shows employers that your ability to tackle technical challenges on a large scale.
Google IT certification is a great opportunity to demonstrate your expertise and to prove your commitment.
You'll also gain access to exclusive content from Google, including updates to our developer documentation and answers to frequently asked questions.
Google IT certifications can be obtained online or offline.
Statistics
- The IT occupation with the highest annual median salary is that of computer and information research scientists at $122,840, followed by computer network architects ($112,690), software developers ($107,510), information security analysts ($99,730), and database administrators ($93,750) (bls.gov).
- The top five regions contributing to the growth of IT professionals are North America, Western Europe, APJ, MEA, and Central/Eastern Europe (cee.com).
- The median annual salary of computer and information technology jobs in the US is $88,240, well above the national average of $39,810 (bls.gov).
- The top five countries contributing to the growth of the global IT industry are China, India, Japan, South Korea, and Germany (comptia.com).
- The top five companies hiring the most IT professionals are Amazon, Google, IBM, Intel, and Facebook (itnews.co).
- The United States has the largest share of the global IT industry, accounting for 42.3% in 2020, followed by Europe (27.9%), Asia Pacific excluding Japan (APJ; 21.6%), Latin America (1.7%), and Middle East & Africa (MEA; 1.0%) (comptia.co).
External Links
How To
How do I start learning cyber security?
Hacking is a term that many people who have worked in computer technology for a long time are familiar with. But they might not be able to define hacking.
Hacking refers to attempts to gain unauthorized access to computers, networks, or other systems by using techniques such as viruses, worms, trojans, spyware, etc.
Cybersecurity has evolved into an industry, offering ways to protect yourself from these types of attacks.
Understanding how hackers work is key to understanding how to keep yourself safe online. Below are some resources to help you get started in your quest to learn more about cybercrime.
What Is Cyber Security?
Cyber security is protecting computers from outside threats. Cyber security is the protection of computers from outside threats. Hacking into your system could allow someone to gain access to files, data, and money.
There are two types: Computer Forensics or Computer Incident Response Teams (CIRT).
Computer forensics is the process of analyzing a computer following a cyberattack. It's done by experts who search for evidence that will lead them to the attacker responsible. Computers are analyzed for signs of tampering or damage caused by malware or viruses.
The second type of cybersecurity is CIRT. CIRT teams collaborate to respond to computer-related incidents. They draw on their collective experience to stop attackers from causing significant damage.